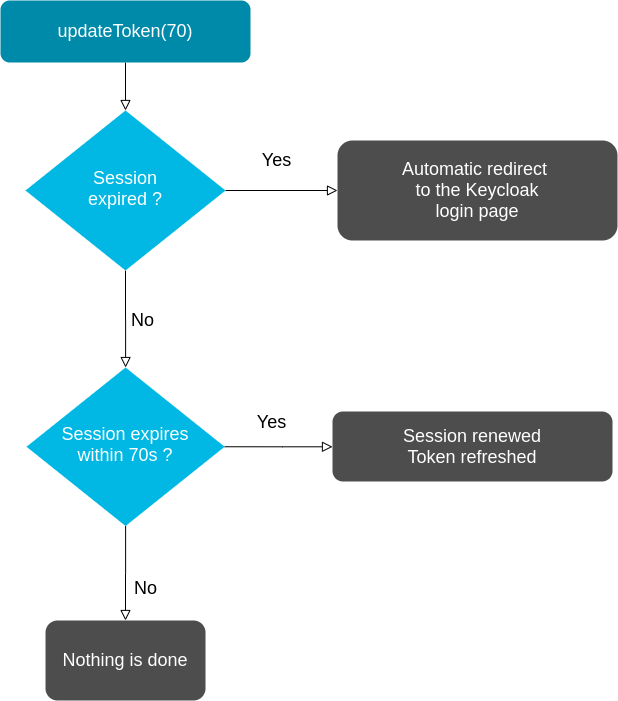
reactjs - Keycloak javascript adapter how to get token api call values back into code - Stack Overflow

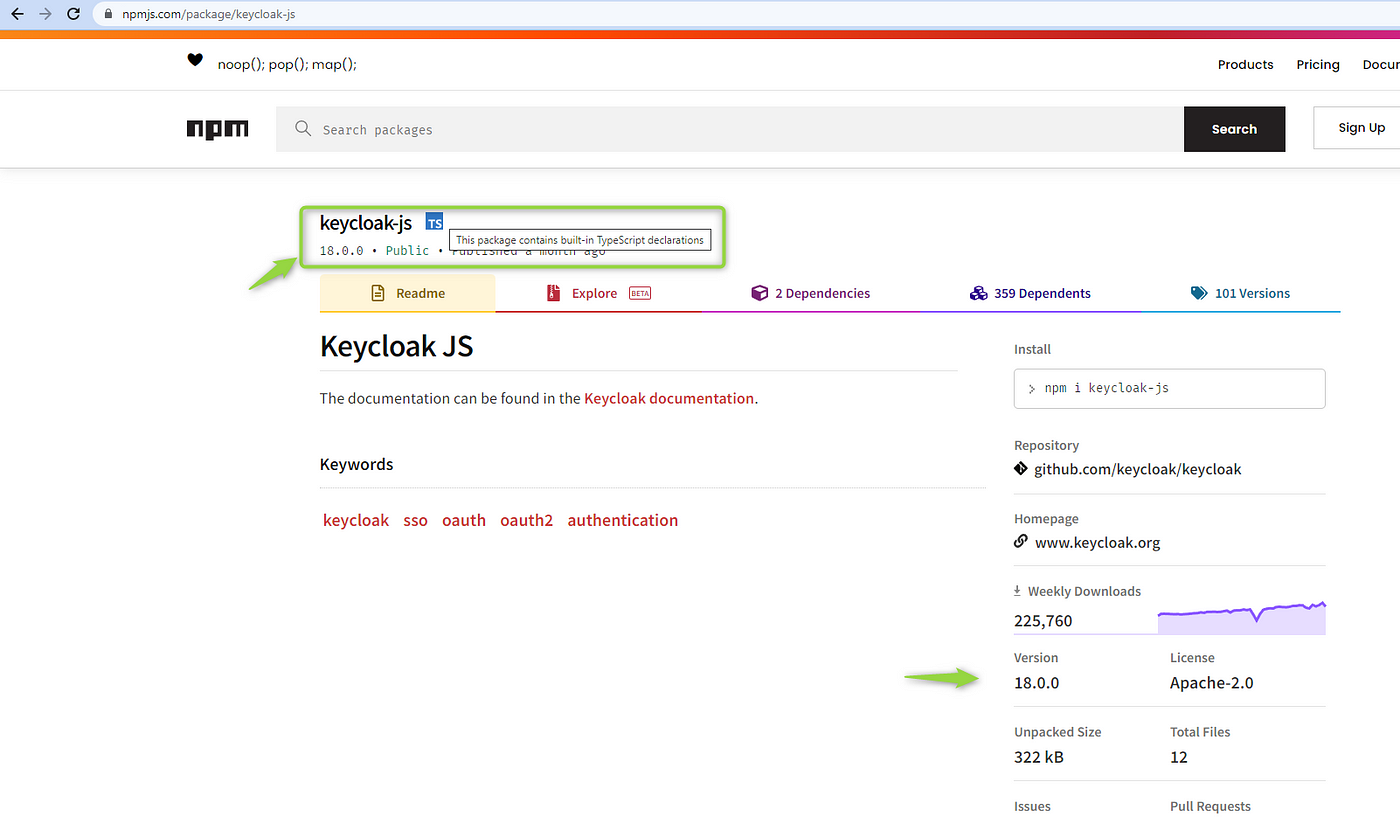
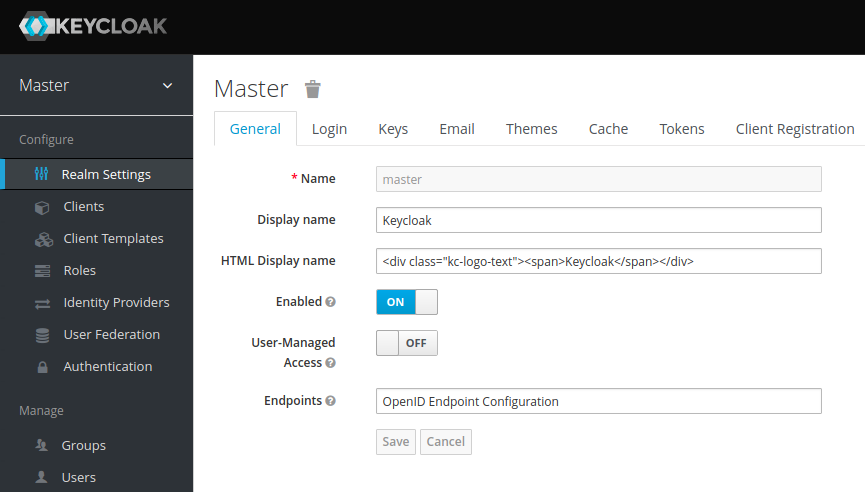
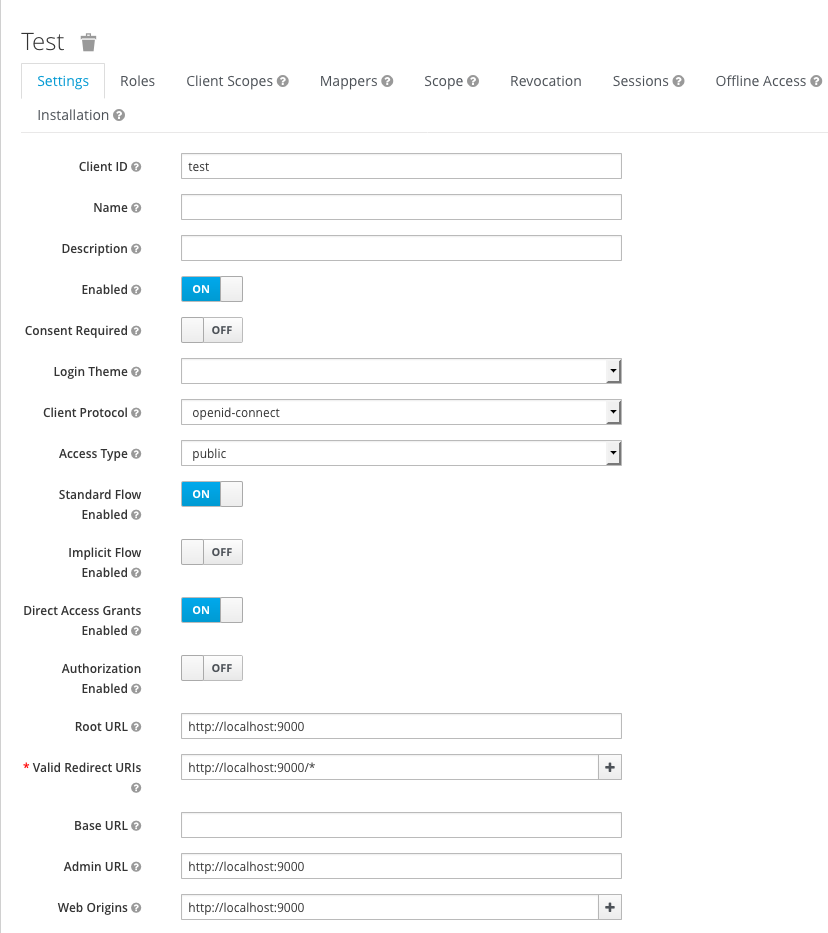
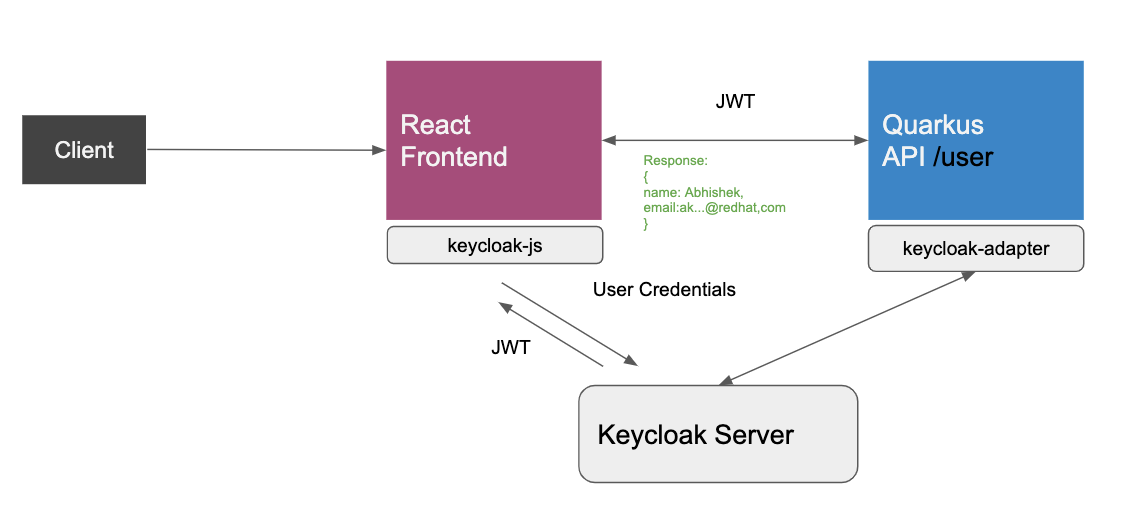
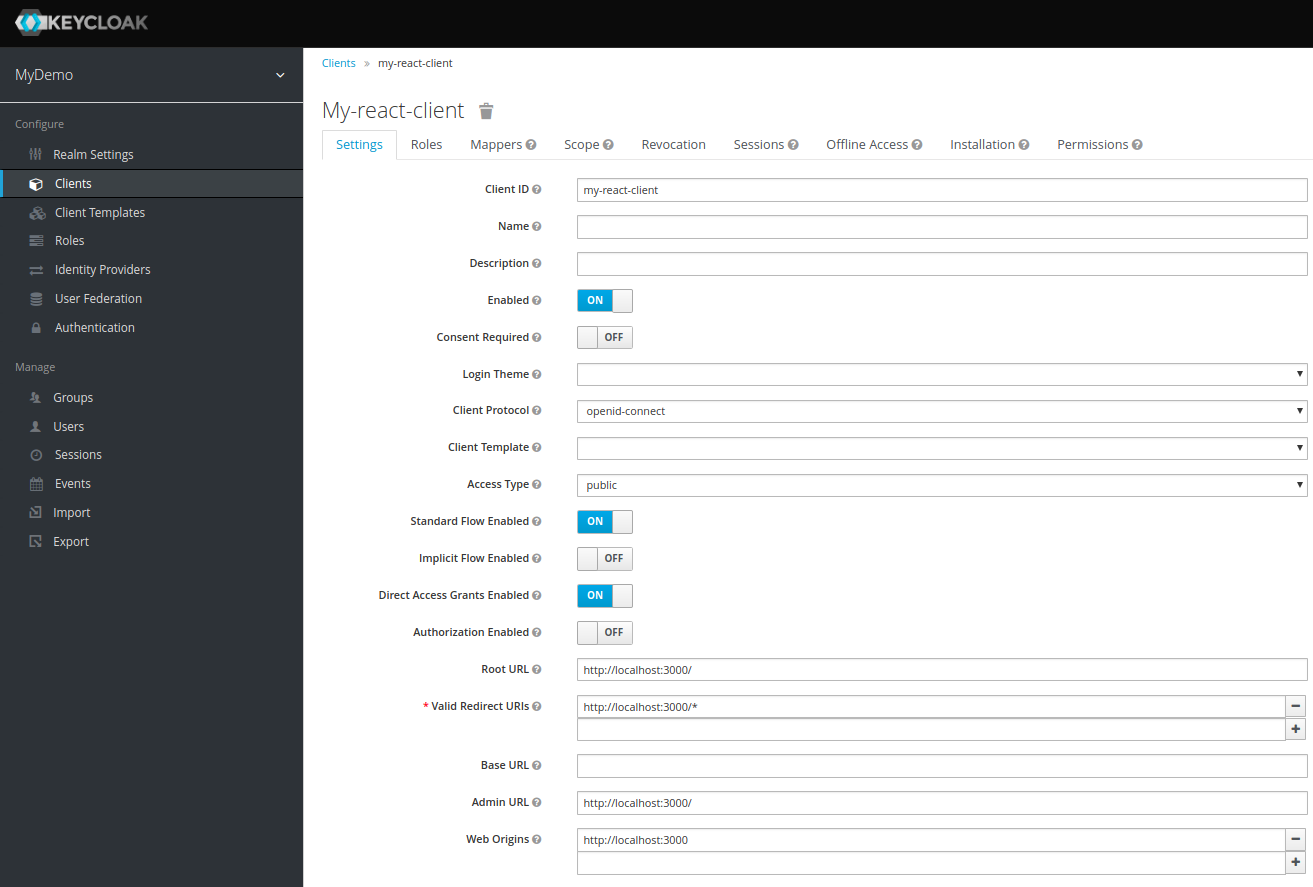
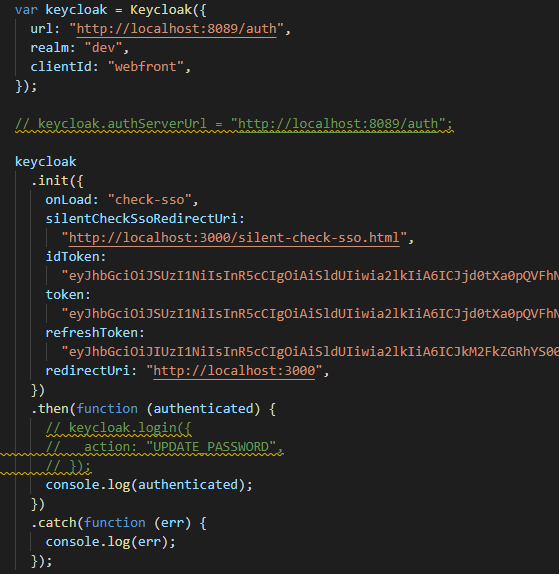
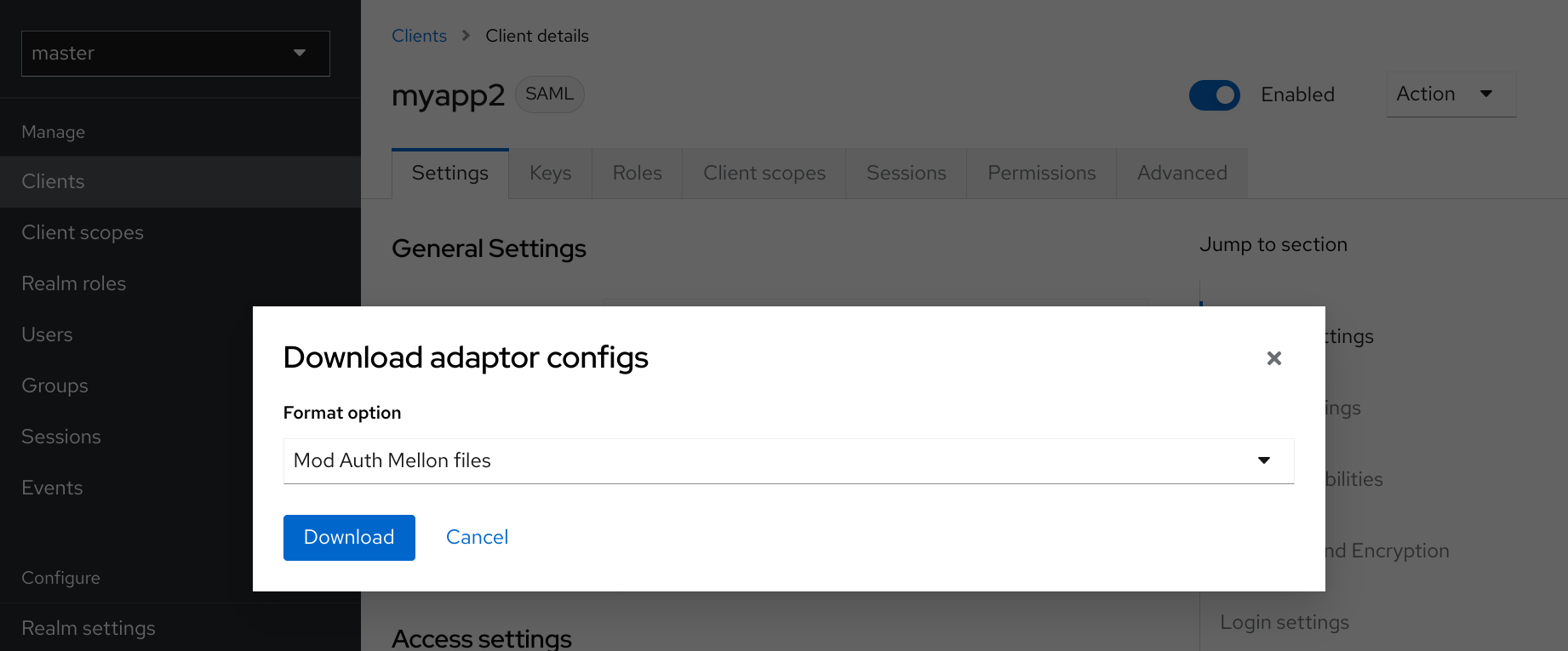
Secure React App with Keycloak. In this post, we will see how to… | by Abhishek koserwal | Keycloak | Medium
Secure React App with Keycloak. In this post, we will see how to… | by Abhishek koserwal | Keycloak | Medium
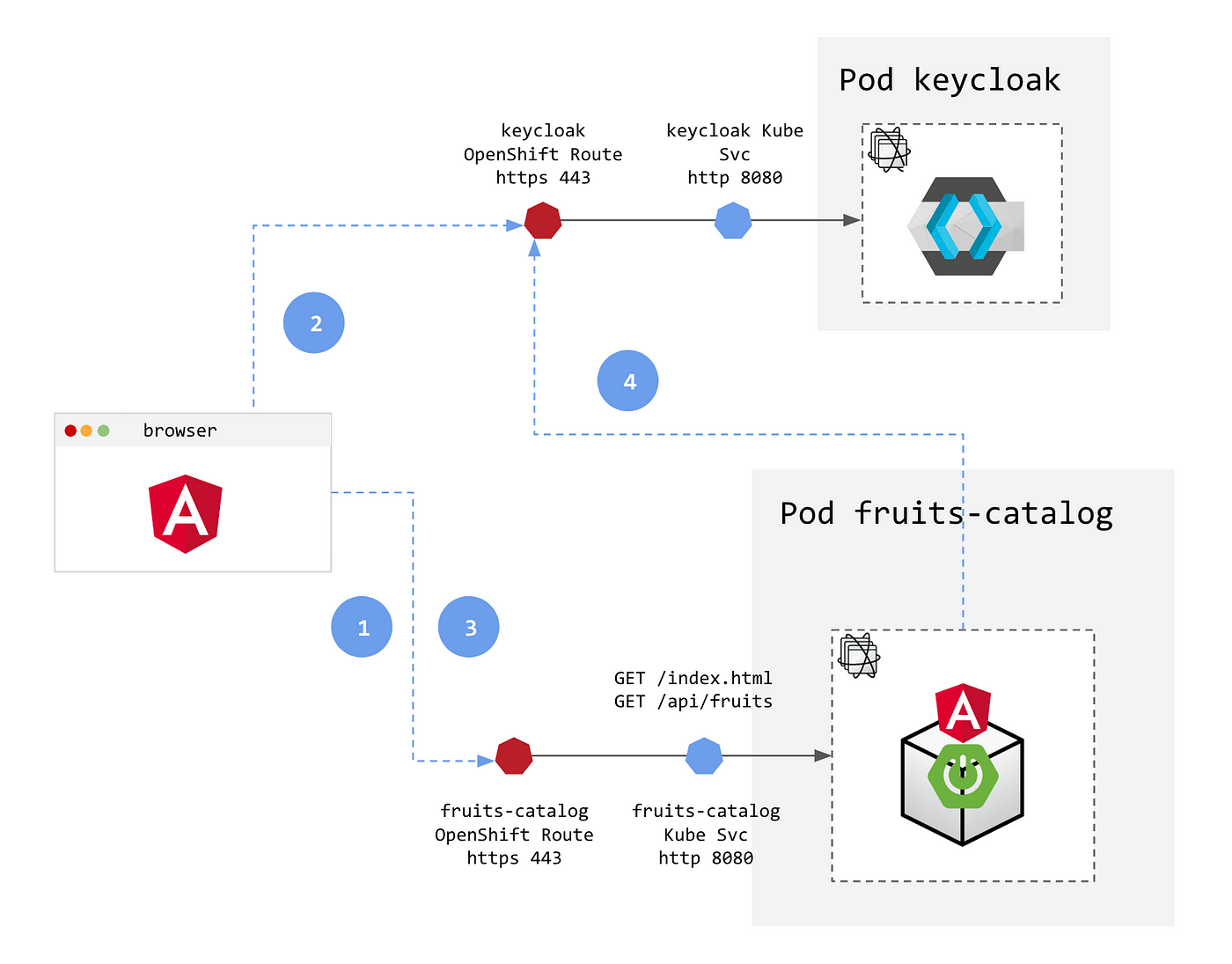
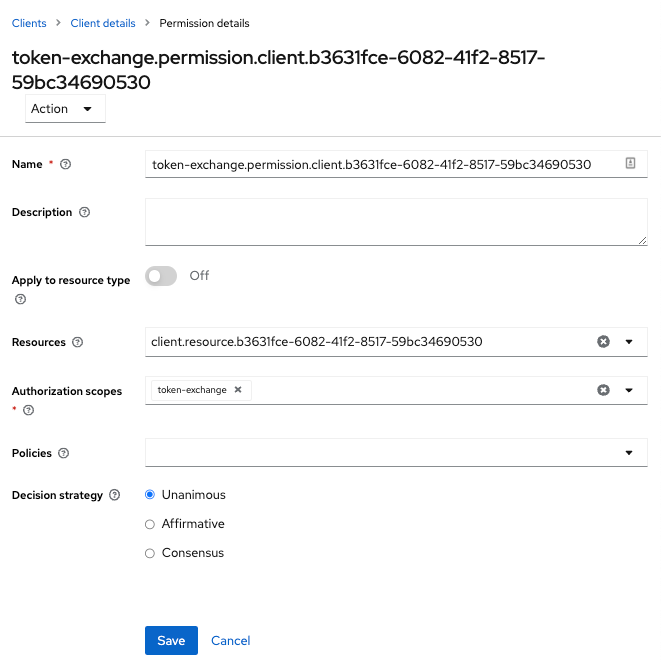
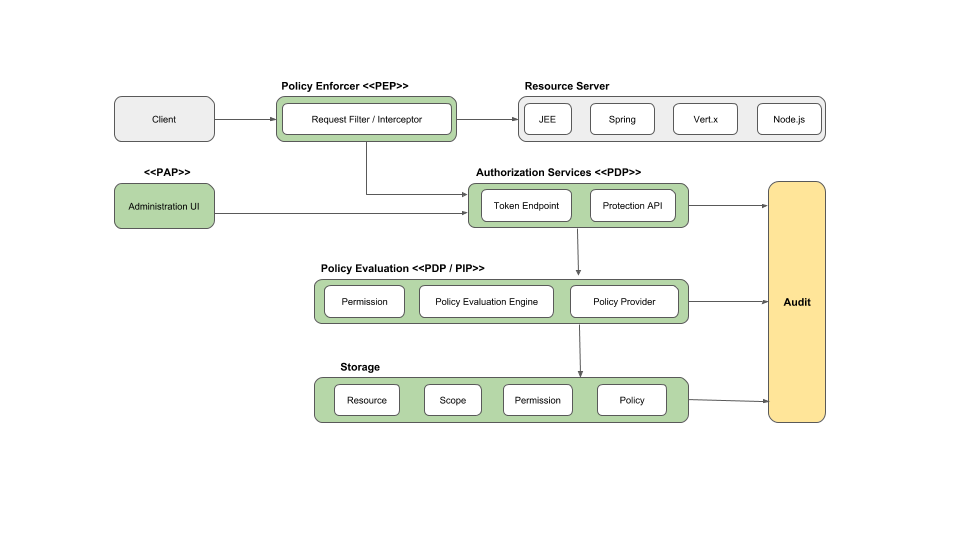
Adding security layers to your App on OpenShift — Part 2: Authentication and Authorization with Keycloak | by Laurent Broudoux | ITNEXT
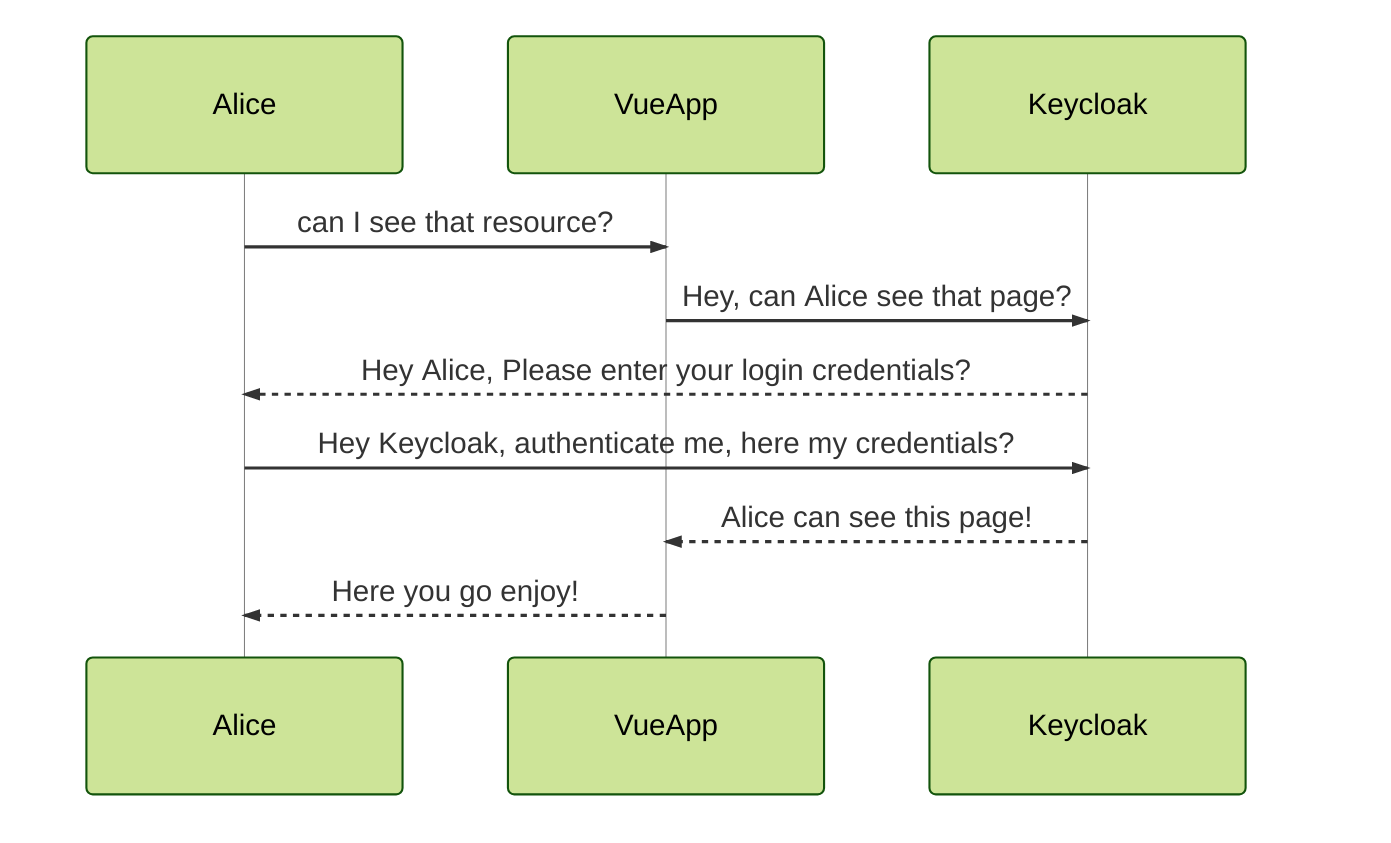
Secure Vue.js app with Keycloak. In this post, we will see how to… | by Abhishek koserwal | Keycloak | Medium